Hey, recently I tried to setup Wireguard on vps with Debian 10 (as a server) and my laptop with EndeavourOS (as a client) and I decided to write it up, so someone may make use of it.
Server setup (Debian 10 buster)
Installing stuff
On Debian wiki we can find information that for Debian buster wireguard is available from Backports. As wiki says on another page, backports are recompiled packages from testing and unstable repository that cane be run on stable Debian distribution. But before we install wireguard from backports we need to perform some steps.
On the server’s terminal type sudo apt edit-sources, you will be asked for editor in which you will add entry to the /etc/apt.sources.list. Then append this line to the opened file:
deb http://deb.debian.org/debian buster-backports main contrib non-free
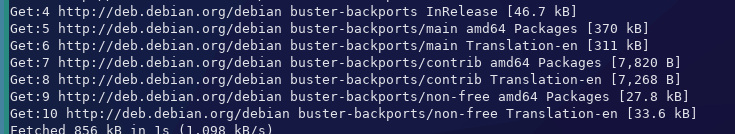
And run sudo apt update, you should see added repositories like on the screenshot below:
If you don’t have dkms installed, install with command sudo apt install dkms (I had problem with not loading wireguard module and lack of dkms was probably the problem; I needed to reinstall wireguard).
Then for installing wireguard copy paste (or type by yourself) this:
$ sudo apt -t buster-backports install wireguard wireguard-dkms
After installing wireguard you can check if wireguard module was added with sudo dkms status (should print something like: wireguard, 1.0.20200908: added)
Configuring
Firstly, we need to generate keys, so we cd as root to /etc/wireguard and then use wg (’#’ in snippet below means that we are running command as root):
$ sudo su
# cd /etc/wireguard/
# umask 077
# wg genkey | tee privatekey | wg pubkey > publickey
# exit
Using umask 077 means that files will be created with mode 600 - only owner (root) can read and write these files.
Private key is generated with wg genkey, running it like that would print that key to the standard output (stdout), so we pipe it to tee privatekey. With tee private key is read from standard input (stdin) and written again to stdout and to thebnew file called privatekey. Then that private key is used (via stdin) by wg pubkey to create public key and save it to file to publickey.
For the next step we will need to get server’s private key, so sudo cat /etc/wireguard/privatekey and copy output!
And now open wg0.conf with text editor of your choice (I’m using vim):
sudo vim /etc/wireguard/wg0.conf
And paste the config:
[Interface]
Address = 10.0.0.1/24
SaveConfig = true
ListenPort = 51820
PrivateKey = key
Change key to copied private key of server. You can also change port or address.
If you have firewall installed you should configure for allowing communication via port set in wg0.conf.
For ufw:
$ sudo apt install ufw # for installing ufw
$ sudo ufw allow OpenSSH # for connecting via ssh with server
$ sudo ufw allow 51820/udp
$ sudo ufw enable
$ sudo ufw status # for checking if ufw is running, its config
Now you should be able to start tunnel with command sudo wg-quick up wg0.
However, I ran into this issue:
[#] ip link add wg0 type wireguard
RTNETLINK answers: Operation not supported
Unable to access interface: Protocol not supported
[#] ip link delete dev wg0
Cannot find device "wg0"
In my case, rebooting the server worked. If rebooting didn’t help you, you may find other possible solutions in this reddit comment.
You can check some info about tunnel with sudo wg show wg0
To stop tunnel you only need to type sudo wg-quick down wg0
Also there is option to start the tunnel with systemctl: sudo systemctl start wg-quick@wg0.
And for starting at boot: sudo systemctl enable wg-quick@wg0.
Status of service can be checked with systemctl status wg-quick@wg0.
Client setup (EndeavourOS)
For Arch based distros, you can install needed stuff with:
sudo pacman -S wireguard-tools
Note: If you use kernel < 5.6, you have to install some additional packages
Next step is creating config file and generating key pair
umask 077
sudo touch /etc/wireguard/wg0.conf
wg genkey | sudo tee /etc/wireguard/privatekey | wg pubkey | sudo tee /etc/wireguard/publickey
Then edit the config:
sudo vim /etc/wireguard/wg0.conf
With lines below:
[Interface]
PrivateKey = priv_key_of_client
Address = 10.0.0.2/24
[Peer]
PublicKey = pub_key_of_server
Endpoint = address_of_server:51820
AllowedIPs = 0.0.0.0/0
Change:
- priv_key_of_client to key from /etc/wireguard/privatekey
- pub_key_of_server to public key of server! (on the Debian run
sudo cat /etc/wireguard/publickey) - address_of_server to IP of Debian server
You may also use different address of interface or port of endpoint (address has to belong to the subnet declared in server’s config, port needs to be the same as in server’s config).
Now on the server, you need to stop tunnel (if have one running, sudo wg-quick down wg0 or sudo systemctl stop wg-quick@wg0) and append Peer to the /etc/wireguard/wg0.conf:
[Peer]
PublicKey = pub_key_of_client
AllowedIPs = 10.0.0.2/24
Change pub_key_of_client to client’s public key and start wg0 on server (sudo wg-quick up wg0 or sudo systemctl start wg-quick@wg0)
Then you should be able to connect on client with command: sudo wg-quick up wg0
To check if tunnel works ping 10.0.0.1 from client (change to the IP you set in server’s /etc/wireguard/wg0.conf in Interface’s Address).
If try ping 1.1.1.1, you will that you have 100% packet loss. For accessing Internet from client (when connected to server via wireguard tunnel), we need to perform some more steps.
Firewall rules + IP forwarding
Firstly, it’s needed to enable IPv4 forwarding with sysctl (sysctl allows for changing kernel parameters at runtime).
Create/open an file:
sudo vim /etc/sysctl.d/10-wireguard.conf
And paste:
net.ipv4.ip_forward=1
Save file and run (as sysctl –help says, it will read values from our created file):
sudo sysctl -p /etc/sysctl.d/10-wireguard.conf
Now we need to once again edit server’s /etc/wireguard/wg0.conf, this time we will append this to the [Interface] section:
PostUp = iptables -A FORWARD -i %i -j ACCEPT; iptables -A FORWARD -o %i -j ACCEPT; iptables -t nat -A POSTROUTING -o eth0 -j MASQUERADE
PostDown = iptables -D FORWARD -i %i -j ACCEPT; iptables -D FORWARD -o %i -j ACCEPT; iptables -t nat -D POSTROUTING -o eth0 -j MASQUERADE
Note: You may have to change eth0 to other interface that is connected to Internet on your server
I copy-pasted these lines from Arch Wiki and they do their job.
But you may find more information about those iptables rules in this cyberciti.biz article.
Last steps are restarting tunnel on server (eg. sudo systemctl restart wg-quick@wg0) and checking if ping 1.1.1.1 works on client.
Resources
I wouldn’t setup WireGuard tunnel without information from these lovely sites:
- Debian wiki about WireGuard
- Debian wiki about Backports
- nixCraft: Debian 10 set up WireGuard VPN server
- Linode: Set Up WireGuard VPN on Debian (they used Debian 9)
- Linuxize: How to Set Up WireGuard VPN on Ubuntu 20.04
- WireGuard Quick Start
- nixCraft: What is Umask and How To Setup Default umask Under Linux?
- Arch wiki about WireGuard